Top Reasons Companies Fail DCSA Security Reviews
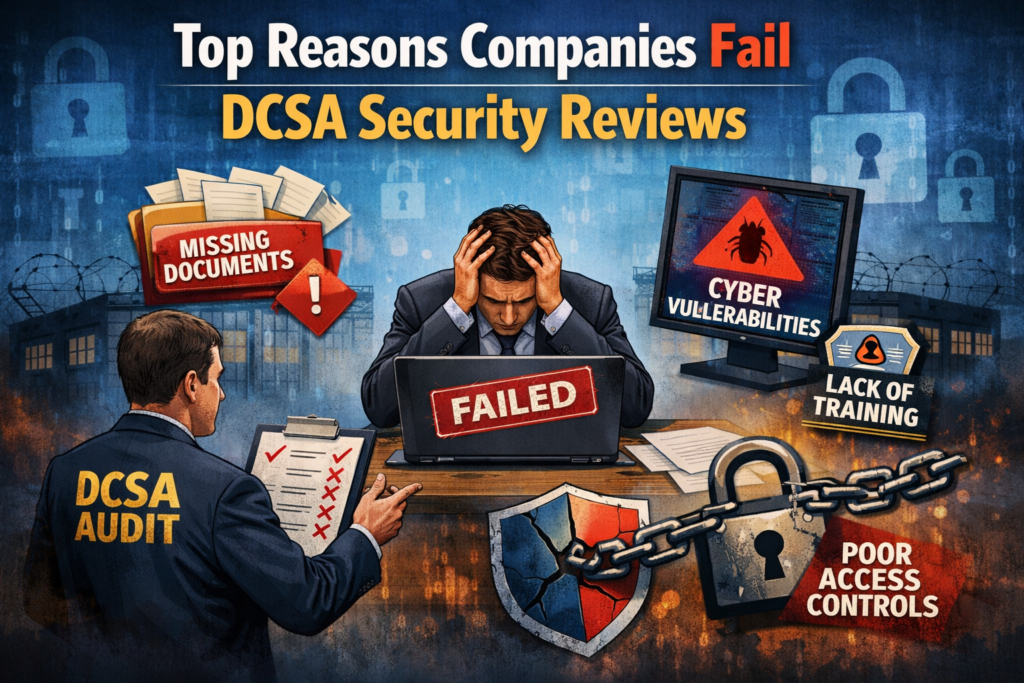
Completing a DCSA security assessment is not simply checking off “completed”, but proving that your institution has the knowledge necessary to secure sensitive information, control risk, and operate within a disciplined framework. Many entities enter the assessment believing that they are ready, only to find that there are identified gaps that could create a delay in operations, a request for remediation plan(s), or failure during the security assessment. Many times, these issues are the cumulative result of specific issues that have occurred as opposed to an isolated issue.
The commonality of these issues often is the result of poor documentation practices, inconsistent application of practices, and a lack of understanding of the requirements. Moreover, if organizations can better comprehend where there may be potential deficiencies, they can prepare themselves for upcoming DCSA assessments and/or avoid incurring costs/errors related to these issues.
Weak or Incomplete Documentation
Weak documentation is one of the primary reasons that companies experience difficulties when undergoing DCSA security evaluations. Though most organizations may have a process for completing a task, the steps may not have been documented in writing, or the dated documents are no longer current. Reviewers want to see written documentation that describes the policies and procedures, documents that show how the company manages security. If there is little or no documentation and/or the documentation is not consistent, reviewers become concerned that controls and procedures are not being implemented as they were intended.
A second issue, and another source of risk to DCSA reviewers, is when there is documentation available on a policy/procedure, but the policy/procedure does not match the actions/duties of employees. For example, an employee may record a visitor according to an informally set process; however, the employee’s procedure could be at odds with the policy. The inconsistency in the application of work procedures and the documentation provided to the reviewer creates risk.
Documentation is necessary for Security compliance; however, the documentation should also depict the actual practices performed in order for the employee to perform the function, and it should be updated as processes change.
Companies do not recognize how important version control and approval of documentation are to creating the appearance that documents are actively managed. The absence of clear ownership or revision history of a document creates uncertainty with regard to accountability and governance, both of which are importantly evaluated as part of an organization’s DCSA review.
Poor Physical Security Implementation
Organizations often do not realize physical security issues until they are subjected to a review. Many organizations think that they are secure because they have locks on exterior doors and use badge access control. DCSA will, however, conduct a more in-depth analysis of your organization’s physical security. They will evaluate your organization’s access control methods, visitor management controls, alarm systems, and controlled area protection.
Many organizations have developed and implemented a set of physical security policies and procedures that dictate the organization’s physical security practices; however, many organizations have trouble enforcing their physical security policies consistently throughout their organization. For example, some employees can allow unauthorized persons into a restricted area by allowing others to enter behind them (tailgating), and others do not properly escort visitors when they enter the facility. These types of behaviors indicate that physical security is not a priority for an organization’s daily operations. Even if an organization has invested in state-of-the-art physical security measures, such as RFID, if those measures are not consistently enforced throughout the organization, then those security measures will not provide the organization with a sense of safety and security.
Another physical security issue that arises in many organizations is the failure to properly distinguish between controlled and uncontrolled spaces. In some cases, organizations fail to establish clear lines of demarcation between controlled and uncontrolled spaces. As a result, reviewers will conclude that there is not enough separation of sensitive information from the organization’s non-sensitive information.
Lack of Employee Training and Awareness
Security operations are as secure as those of the people working them. Training is mandated as part of DCSA compliance and is often viewed as one of the least important aspects by many organizations. Employees must be trained in their obligations regarding reporting incidents and dealing with sensitive information. When reviewers are encountered, they look into the responses given; thus, if employees provide some unsatisfactory responses to elementary questions, it gets noted and adversely affects their comments.
Many companies’ training programs do not become successful because they are seen as one-time only events. While new hire orientation training may occur, periodic training sessions for the same employees are usually skipped or neglected. Over time, employees forget procedures they learned earlier or decide to create shortcuts. Ongoing training is required to make the employee aware of what is expected of them in relation to security and provide employees with a consistent way of performing security measures from one operation to another.
Another training-related issue is the difference between role-specific training and basic security training. Individuals with controlled access should receive more specific and extensive training than those in non-permissive roles. If everyone receives only the same basic training, auditors may make the assumption that appropriate employees in high-risk roles have not received adequate preparation. Successful training programs have materials for each role that are based upon each role’s specific requirements and contain records of the training conducted for each individual.
Inconsistent Insider Threat Program
The Insider Threat Programs are vital components of DCSA reviews, yet this is an area where many organizations are deficient. While organizations may have an Insider Threat Program in place on paper, they may not have implemented it fully. Therefore, reviewers expect to find established monitoring, reporting, and coordinated procedures across multiple departments.
One of the common deficiencies found among organizations is limited communication between the security, human resources, and upper management areas. Since insider threat programs require the sharing of information, missing out on collaborating can prevent key indicators of potential incidents from being identified. Examples of this type of communication problem include a behavioral change or a policy violation not being referred to the correct department.
In addition to poor coordination due to the lack of communication, there is typically also a major gap in documentation. Organizations will have discussions about their concerns with respect to an insider threat; however, they may fail to document their follow-up actions. Reviewers are looking for evidence that a program is both active and operating as intended. Examples of documentation that indicate the level of maturity and commitment of an organization include: meeting minutes, training records, and documentation related to the tracking of cases through their investigative processes.
Conclusion
Most DCSA security reviews do not have a single reason for failure, but result from a combination of poor documents, inconsistent application of standards, lack of training, weak insider threat programs, and limited oversight. Dive Deep Security offers services to assist organizations in preparing for the DCSA security review process, identifying their areas of weakness, enhancing documentation, and implementing reasonable security controls to survive scrutiny of a real-world evaluation.
Frequently Asked Questions
A DCSA security review evaluates whether a cleared contractor complies with the National Industrial Security Program (NISP) requirements for protecting classified information, systems, and facilities. Reviews may include document checks, interviews, and facility walkthroughs.
Poor implementation of the security program, companies often have policies written but not actually followed. DCSA focuses on execution, not just documentation.
Companies fail when:
- Annual refresher training is missing
- New hires aren’t trained before access
- Insider threat training not documented
- Training records incomplete
DCSA expects documented, role-based, and recurring training.
